Develop the right mindset for Rails security
Avoid shipping vulnerable code by learning how to prevent security issues in your Rails applications.
Get the course for $99You are a security concious developer and you follow the advice given by security folks to have strong password requirements, and you set a rule of having at least 10 characters, containing one uppercase, one lowercase letter, at least one digit and special character. Surely, this will result in strong passwords, right?
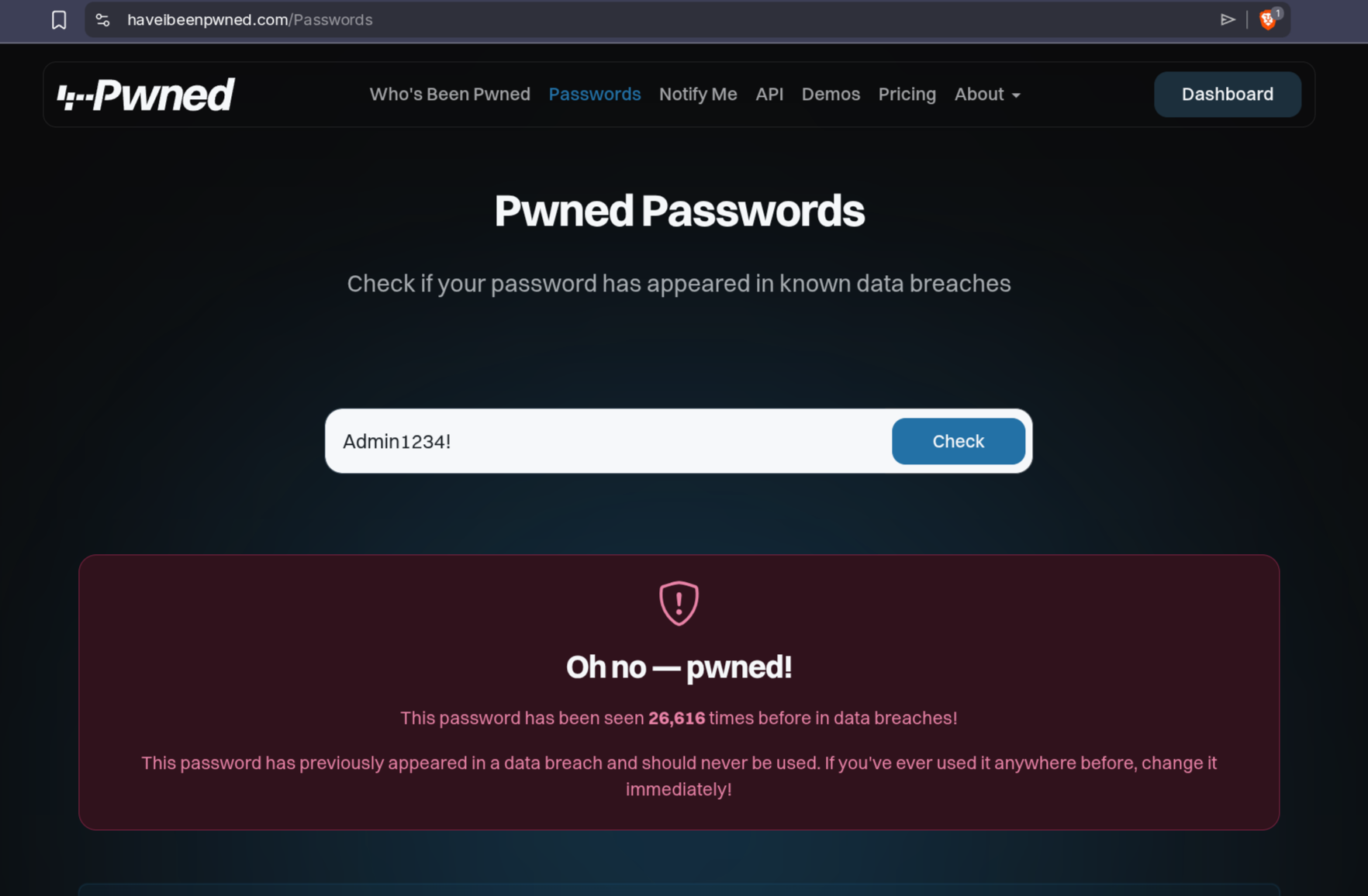
Well, “Admin1234!” satisfies these requirements, and to be fair, it isn’t an easy to bruteforce password in a traditional way, but it follows a predictable pattern, and any serious password cracking attempt would use a list, built from such pattern. Also, if you check this password in data breaches, you will see that it has been found plenty of times:
As I mentioned, the issue with password like this is the recognizable pattern, so a good password strength estimator should tackle the problem from that angle. The zxcvbn password strength estimator does just like that. It uses dates, words, etc and patterns to verify the strength of a password. This is actually much better than the earlier requirements, because as I mentioned Admin1234! matches the rules, but is a weak password, while “U2wNiF7QN” fails the rules, but in reality much harder to crack. This tool has implementations in multiple languages, so you can easily do a frontend and backend validation with the same rules.
The haveibeenpwned API is also a great option to exclude password that been in a leak before, the only downside is the extra network request, but it is a good strategy to do that check every X login attempts only, and warn the user in case there is a match.
Do youself a favor, and start using these methods, you will prevent account take over attacks against your users.